🤔 Why self-host your AI services?
Before diving into the technical details, let's ask the fundamental question: why go to the trouble?
Privacy and data sovereignty
When you use a standard cloud service, your data passes through third-party servers. Your prompts, your files, your conversations — everything is potentially accessible to the provider.
With self-hosting:
- Your data stays on YOUR server
- No third party has access to your prompts or results
- Simplified GDPR compliance (you know exactly where the data is)
- No resale of your data to train models
Total control over infrastructure
| Aspect | Cloud/SaaS | Self-hosted |
|---|---|---|
| Uptime | Depends on the provider | You decide |
| Updates | Forced | At your own pace |
| Configuration | Limited | Total |
| Customization | Depending on the plan | Infinite |
| Data | On their side | On your side |
Controlled costs
A VPS for €5-15/month easily replaces several SaaS subscriptions that would cost €50-100/month combined. We break down the real costs further down.
Learning and skills
Self-hosting is also about upskilling in Linux, networking, security, and deployment. Skills that are worth their weight in gold on the job market.
🖥️ Choosing your VPS: minimum specs
Not all VPS are created equal. Here is what you need to comfortably run an AI setup.
Minimum recommended specifications
| Component | Minimum | Recommended | Why |
|---|---|---|---|
| vCPU | 2 cores | 4 cores | API calls and parallel processing require CPU |
| RAM | 4 GB | 8 GB | Python + Node.js + database = resource-hungry |
| Storage | 80 GB SSD | 160 GB NVMe | Logs and AI data grow quickly |
| Bandwidth | 1 TB/month | Unlimited | API calls consume bandwidth |
| OS | Ubuntu 22.04+ | Ubuntu 24.04 LTS | Long-term support, massive community |
Which provider to choose?
After testing several hosts, here is our recommendation:
Hostinger VPS is our #1 choice for value for money. With a 20% discount via our link, you get a high-performance VPS for the price of a coffee per month.
| Provider | Price/month | vCPU | RAM | Storage | Our verdict |
|---|---|---|---|---|---|
| Hostinger 🏆 | ~5-10€ | 2-4 | 4-8 GB | 80-200 GB NVMe | Best value for money, -20% with our link |
| Hetzner | ~5-15€ | 2-4 | 4-8 GB | 40-160 GB | Excellent, EU datacenters |
| OVH | ~6-12€ | 2-4 | 4-8 GB | 80-160 GB | French, good performance |
| DigitalOcean | ~12-24$ | 2-4 | 4-8 GB | 50-160 GB | Simple but more expensive |
| Contabo | ~5-10€ | 4-6 | 8-16 GB | 200-400 GB | Generous specs, average support |
💡 Tip: start with a 2 vCPU / 4 GB RAM plan. You can always upgrade later. With Hostinger and the 20% discount, it comes to less than 6€/month.
🔧 Setup initial Ubuntu : the foundations
You have your VPS? Perfect. Here is how to set it up properly right from the start.
Step 1: First SSH connection
# Connect with the root password provided by the host
ssh root@VOTRE_IP_VPS
# First thing: update the system
apt update && apt upgrade -y
Step 2: Create a non-root user
NEVER work as root on a daily basis. This is the number one rule of server security. Create a deploy user, add them to the sudo group, then copy your public SSH key into their .ssh directory while respecting strict permissions (700 for the directory, 600 for authorized_keys).
Step 3: Secure SSH
# Edit the SSH config
nano /etc/ssh/sshd_config
In the configuration file, modify the following settings: disable root login (PermitRootLogin no), disable password authentication (PasswordAuthentication no), change the default port (for example Port 2222), and limit authorized users (AllowUsers deploy). Then restart the service with systemctl restart sshd.
⚠️ Important: before closing your root session, open a NEW terminal and test the connection with the
deployuser. If it doesn't work, you still have the root session to fix it.
Step 4: UFW Firewall
UFW (Uncomplicated Firewall) is your first line of defense. Configure it to block all incoming traffic by default, only allow necessary ports (SSH on your custom port, HTTP 80 and HTTPS 443), then enable it.
Step 5: Fail2ban against brute-force attacks
Fail2ban monitors logs and bans IPs that attempt repeated connections. Install it via apt, then create a local configuration file (jail.local) to define a prolonged ban time (86400 seconds), a maximum of 3 attempts, and the ufw action to block offenders at the firewall level.
Step 6: Automatic updates
Security vulnerabilities don't wait. Install unattended-upgrades via apt and configure it with dpkg-reconfigure. In the /etc/apt/apt.conf.d/50unattended-upgrades file, make sure to allow security updates and standard updates, then enable automatic reboot during off-peak hours (for example 04:00).
🏗️ Services to host
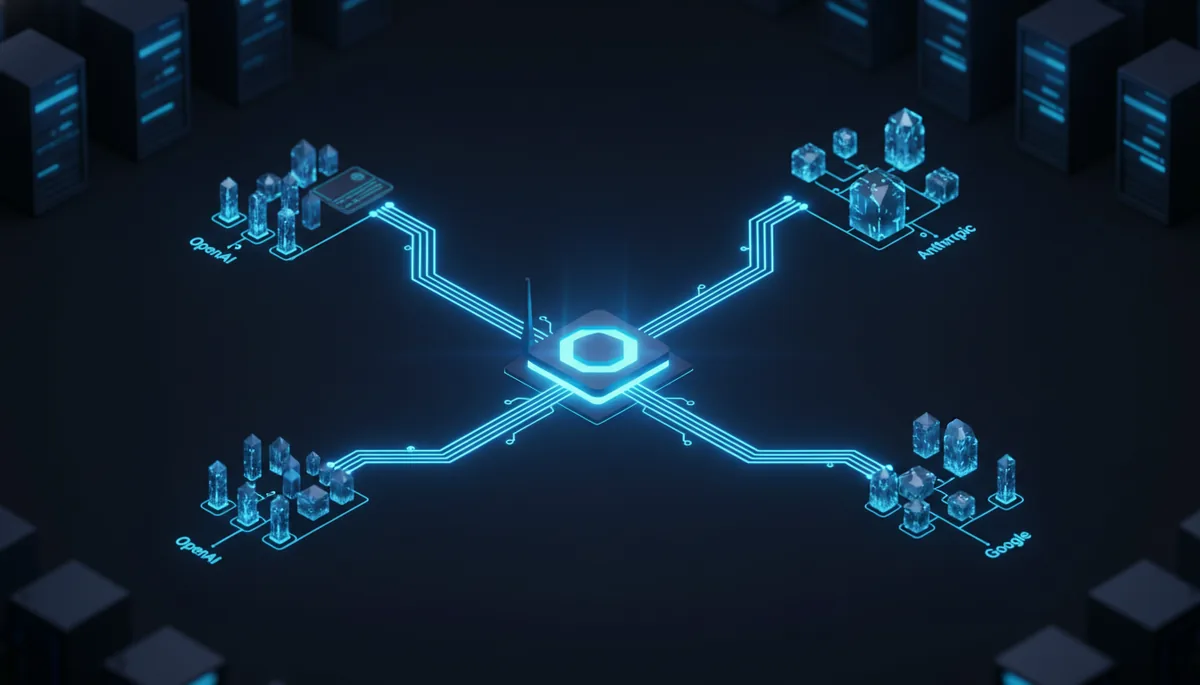
Now that the server is secured, let's install the services. Here is the target architecture: internet traffic arrives on a reverse proxy (Caddy or Nginx) listening on port 443, which handles SSL and distributes requests to three local services. OpenClaw (on port 3000) acts as the central AI agent, FastAPI (on port 8000) handles your custom endpoints, and a SQLite Web interface (on port 8080) allows you to visually explore the database.
OpenClaw: your central AI agent
OpenClaw is the brains of the operation. It is the AI agent that orchestrates everything. To understand how to connect it to the best models, check out our guide AI APIs: OpenRouter vs direct calls.
OpenClaw requires a Node.js environment version 20 or higher. Installation is done via the npm package manager by first adding the official NodeSource repository to your system's apt sources, then installing the openclaw global package. Once in place, the tool is accessible from the command line from any folder.
To isolate your services in containers and simplify management, check out our guide Docker + AI: containerizing your smart services.
For the complete setup, follow our guide Install OpenClaw on a VPS and Configure OpenClaw.
FastAPI: your custom API
FastAPI is perfect for creating custom endpoints that complement your AI setup.
To deploy FastAPI, start by installing Python 3.11 as well as the venv utility via apt. Then, create a dedicated virtual environment (for example in /home/deploy/api-env) to isolate dependencies. In this environment, install the essential packages: FastAPI itself, the uvicorn ASGI server, python-dotenv for environment variable management, and httpx for asynchronous HTTP requests.
Next, create your service in /home/deploy/api/main.py by initializing a FastAPI application with CORS middleware restricted to your domain, a /health endpoint for monitoring, and your custom business endpoints (like /api/stats to return metrics).
Register the service with the system via a systemd unit file (/etc/systemd/system/fastapi.service) that points to the uvicorn executable in your venv, listens on 127.0.0.1:8000, and enables automatic restart in case of a crash. Enable it with systemctl enable --now fastapi.
SQLite: your lightweight database
SQLite is perfect for self-hosting: zero config, zero database server, single file.
# Install SQLite tools and create the data directory
sudo apt install sqlite3 -y
mkdir -p /home/deploy/data
Initialize your /home/deploy/data/app.db database with tables suited to your needs, for example a logs table (id, timestamp, level, message, metadata) and a cache table (key, value, expires_at), remembering to add indexes on frequently queried columns like timestamp or expires_at.
💡 Why SQLite instead of PostgreSQL? For a personal setup/small project, SQLite easily handles millions of rows, consumes almost no RAM, and backups are done by copying a file. PostgreSQL becomes relevant when you need massive concurrent access or advanced features (advanced JSON, advanced full-text search, etc.).
Reverse proxy: Caddy (recommended) or Nginx
The reverse proxy is the entry point to your server. It handles SSL, routing, and security.
Option A: Caddy (recommended for simplicity)
Caddy automatically manages SSL certificates via Let's Encrypt. Zero SSL config. Its installation on Ubuntu is done simply by adding the Cloudsmith GPG key and official repository to your apt sources, then via apt update && apt install caddy -y.
In the /etc/caddy/Caddyfile file, define your domain and routing rules: a handle /api/claw/* block redirecting to localhost:3000, a handle /api/* block to localhost:8000, and a default handle block serving static files from /home/deploy/www. Add security headers (X-Content-Type-Options, X-Frame-Options, Referrer-Policy). Reload the configuration with systemctl reload caddy.
Option B: Nginx
Install Nginx and Certbot (sudo apt install nginx certbot python3-certbot-nginx -y). In /etc/nginx/sites-available/mondomaine.com, configure a server block listening on port 80 with location blocks proxying to your local services (OpenClaw on port 3000, FastAPI on port 8000), making sure to forward the Host and X-Real-IP headers. Enable the site, obtain the SSL certificate with certbot --nginx -d mondomaine.com, then reload Nginx.
💰 Actual monthly costs
Let's talk money. How much does this setup really cost in 2025?
| Item | Monthly cost | Notes |
|---|---|---|
| VPS Hostinger | 5-10€ | With 20% discount via our link |
| Domain | ~1€ | ~12€/year spread out |
| AI APIs (OpenRouter) | 2-15€ | Depending on usage, free models available |
| External backups | 0-2€ | S3-compatible or rsync |
| Total | 8-28€/month |
Comparison with SaaS alternatives
| Service | SaaS | Self-hosted | Savings |
|---|---|---|---|
| AI Agent (ChatGPT Pro) | 20€/month | 0€ (free OpenClaw) | 20€/month |
| API Gateway | 15-50€/month | 0€ (free Caddy) | 15-50€/month |
| Database | 10-30€/month | 0€ (free SQLite) | 10-30€/month |
| Monitoring | 10-25€/month | 0€ (custom scripts) | 10-25€/month |
| Total | 55-125€/month | 8-28€/month | 47-97€/month |
💡 Over a year, self-hosting can save you 500 to 1,100€. The time investment (a few hours of setup) pays for itself very quickly.
📋 Deployment Checklist
Before considering your setup "production-ready", verify each point:
✅ Non-root user created
✅ SSH via key only (password disabled)
✅ SSH port changed
✅ UFW enabled (only 80, 443, SSH open)
✅ Fail2ban configured and active
✅ Automatic updates enabled
✅ Reverse proxy with SSL (valid certificate)
✅ Services in systemd (auto-restart)
✅ Backups configured (at least daily)
✅ Basic monitoring in place
Automatic backup script
Create a script /home/deploy/scripts/backup.sh that performs an atomic backup of your SQLite database via the .backup command, compresses your critical configuration files (Caddyfile, environment variables, jail.local) into a tar.gz archive, and automatically deletes files older than 7 days to limit disk space usage. Schedule its daily execution at 3 AM via crontab -e.
🔒 Going further with security
This guide covers the basics, but security is a continuous process. To go deeper:
- Advanced monitoring: install Netdata or Prometheus + Grafana to monitor performance
- Alerts: configure Telegram notifications when something goes wrong
- Audit: run
lynis audit systemregularly to detect weaknesses - Docker: isolate each service in its container to limit the attack surface
For a complete guide on securing, check out our article Sécuriser OpenClaw. You can also expose your services even more securely thanks to Cloudflare Tunnel : exposer ses services sans ouvrir de ports.
🎯 The Essentials
- Self-hosting your AI on a VPS costs between €8 and €28/month, saving you €500 to €1,100 per year compared to SaaS.
- The pillars of security are: non-root user, SSH via key, UFW, fail2ban, and automatic updates.
- Caddy is the recommended reverse proxy for its automatic SSL management via Let's Encrypt.
- SQLite is more than enough for personal use or a small project, without the complexity of a dedicated database server.
- All your services (OpenClaw, FastAPI) must be managed by systemd to guarantee an automatic restart in case of a crash.
🛠️ Recommended Tools
| Tool | Role | Why we recommend it |
|---|---|---|
| Hostinger | VPS Hosting | Best value for money in 2025 |
| OpenClaw | AI Agent | Centralized orchestration, free |
| Caddy | Reverse proxy | Automatic SSL, simple configuration |
| FastAPI | Custom API | High performance, Python typing, native async |
| SQLite | Database | Zero config, single file, easy backups |
| Fail2ban | Anti brute-force | Essential protection for exposed servers |
| UFW | Firewall | Simple interface for iptables |
❌ Common mistakes
Working as root on a daily basis: This is the number one vulnerability. A malicious script executed as root has total access to your server. Always create a dedicated user with sudo.
Forgetting to test SSH before closing the root session: If you change the SSH port or disable the password without checking in a second terminal, you risk locking yourself out of your own server.
Not setting up backups: An SSD drive will eventually die. Without automated backups of your SQLite database and your configs, a hardware failure = starting over from scratch.
Leaving unnecessary ports open: If UFW is not configured, your server exposes dozens of ports to bots. Only 80, 443, and your SSH port should be accessible from the outside.
Ignoring security updates: In 2025, critical vulnerabilities are exploited within hours. unattended-upgrades are not optional, they are essential.
❓ FAQ
Is my VPS powerful enough to run an LLM?
No, a standard VPS (2-4 vCPU, 4-8 GB RAM) cannot run large models locally. The architecture described in this guide routes requests to external APIs (like OpenRouter) that run the models on their GPUs. Your VPS acts as a secure gateway and hosts the business logic.
Why not use Docker right from the start?
Docker adds a layer of complexity. For an initial setup, installing services directly on Ubuntu allows you to understand each component. Once you are comfortable, containerization with Docker is the logical next step (see our Docker + AI guide).
What to do if my IP is banned by fail2ban?
Log in via your host's VPS console (which doesn't go through SSH), then unban your IP with the command sudo fail2ban-client set sshd unbanip YOUR_IP.
Caddy or Nginx, which one should I really choose?
Caddy if you want automatic SSL without touching the configuration. Nginx if you need advanced features (complex rate limiting, specific streaming, very granular configuration). For 90% of self-hosting AI setups, Caddy is the right choice.
How long does this complete setup take?
Expect around 30 to 45 minutes if you follow this guide step by step without getting stuck.
🎯 Summary: your setup in 30 minutes
- Order a VPS on Hostinger (take advantage of the 20% discount)
- Secure: non-root user, SSH key, UFW, fail2ban
- Install: Node.js, Python, SQLite
- Deploy: OpenClaw, FastAPI, Caddy reverse proxy
- Automate: backups, updates, monitoring
- Enjoy: a complete setup for 8-15€/month
🏁 Conclusion
Self-hosting isn't just for experts. With this guide, you have everything you need to set up a solid, secure, and cost-effective AI server. And the best part? You keep total control over your data and tools. In 2025, with tools like Caddy or FastAPI that greatly simplify deployment, it has never been faster to gain your independence from SaaS giants. Start small, iterate, and upgrade your infrastructure as your needs grow.
To go further with your new environment, discover What is OpenClaw?, follow the guide Install OpenClaw on a VPS, customize it with Configure OpenClaw, or learn how to Secure OpenClaw. To optimize the connection to your models, read AI APIs: OpenRouter vs direct calls, and discover what you can accomplish with Automate your life with AI.